HID stories - Page 6
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Rising cyber threats target social media in New Zealand

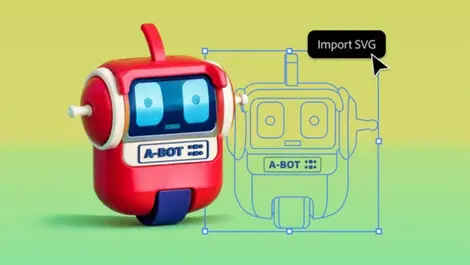
Adobe unveils faster performance & font features in Illustrator
Adobe debuts public beta of 3D design tool Project Neo

BeyondTrust launches AI tool to bolster identity security

FlexibleFerret malware evades Apple's XProtect updates

Mandiant partners with Android team to tackle concealed malware

Braze strengthens ANZ presence with data centre, HQ launch

Gen Z & millennials prioritise quality amid cost crisis

Deepfake threat looms for B2B marketing leaders, says report

Apple launches new app for creating custom invitations

Contec CMS8000 patient monitors pose data security risk, experts warn

AI-fuelled bank scams rise, impersonating officials with ease

Experts warn of security risks as DeepSeek limits new sign-ups

Remote workers logging longer hours than office peers

Cleaning up the chaos and elevating unstructured data value

Malware targets newcomers with Trojan disguised as tool

Game review: Donkey Kong Country Returns HD (Switch)

The AI revolution – security challenges and the critical role of zero trust

AI in healthcare set to revolutionise the industry by 2032
