HID stories - Page 26
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

IWD 2023: Unboxing to build diversity and close the gender gap

Game review: Hogwarts Legacy (PS5)

Fortress Solutions partners with JBG SMITH for 5G Smart City

How outsourcing payroll can deliver a measurable ROI

Wise partners G-P for faster, low-cost contractor payments

Mindvalley launches digital experiences on Storyblok's CMS

Frost Radar: HID recognised for biometric authentication

Dicker Data announces strategic acquisition of Kiwi distie CSP

How organisations can manage supply chain cyber risk and increase their resilience

What is data fabric, and how can you use it?

Check Point, Samsung partner to elevate mobile security

Killnet software given to pro-Russian hacktivists - Radware

Mobile operators urged to be more vigilant against cyberattacks

Why graph analytics is the “next big thing” for data

M-Files top technology predictions for 2023 and beyond

Why deep observability is key to closing cloud migration security gaps
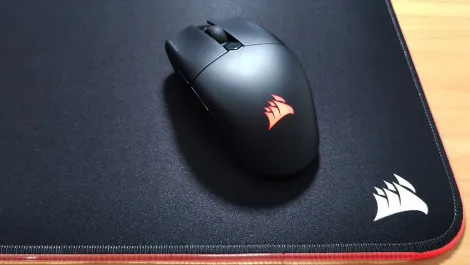
Hands-on Review: Corsair Katar Elite wireless mouse
China-based threat group targeting public cloud - Radware

Cybersecurity priorities for mobile operators in 2023
