HID stories - Page 27
HID is a key player in the physical access control and trusted identity solutions space, focusing on innovations that enhance security, efficiency, and user experience across various sectors. Their work encompasses mobile access technologies, biometric authentication, cloud-based credential issuance, and integration of AI to advance security protocols.
Through their reports and product launches, HID highlights critical trends such as mobile IDs, AI-driven access management, sustainability in security systems, and the shift towards digital and AI-powered credentialing. By exploring HID-related stories, readers can gain insights into the evolving landscape of access control technologies, risk management in cyber and physical security, and the growing emphasis on seamless, secure user authentication methods.
Whether you’re interested in the impact of emerging technologies like AI and biometrics on identity verification or the strategic adoption of cloud solutions to streamline security operations, the content tagged with HID offers valuable knowledge for IT professionals, security managers, and technology enthusiasts looking to stay informed about advancements and challenges in trusted identity and access control.

Lenovo ThinkBook Plus reinvents rotating display form factor

Nokia deploys Orchestration Center software for Telstra

Voice recognition software market to hit $10.5 billion by 2030

TeamViewer digitalise GlobalFoundries warehouse operations
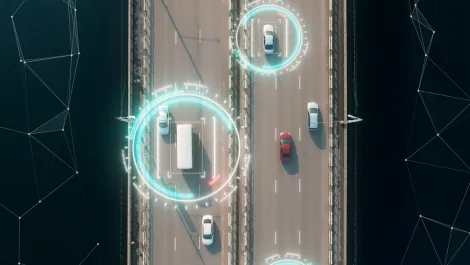
Tech adoption helping fleets navigate operational obstacles

Zimperium teams discover new malware in Flutter developed apps

Digitally transforming is easier when systems communicate

Ribbon Communications appoints Channel UC as ANZ distributor

Video: 10 Minute IT Jams - An update from Wasabi Technologies

Archive file formats discovered as most common way to deliver malware

Zimperium reveals new Android threat 'the Schoolyard Bully'

Lookout finds predatory behaviour on 300 loan apps

Forescout's Vedere Labs details OT vulnerabilities in latest study

Sophos report reveals stark reality of cybercrime-as-a-service

Building a targeted operating cybersecurity model

Twelve social media threats to watch for in 2023

Hands-on Review: Asus CM3 Chromebook

Hands-on Review: Norton Identity Advisor Plus

Kaspersky researchers uncover previously unknown cyber threats